The world’s most widely used JavaScript libraries—downloaded billions of times each week—have been compromised in a supply chain attack that underscores the fragility of opеn-source infrastructure. A single phishing email was all it took to breach the account of a prominent developer, opening the door for malicious code to spread through projects that underpin much of the modern web.
Key Points
- Phishing breach: Developer account hijacked, injecting malware into packages with billions of weekly installs.
- Crypto theft limited: Arkham Intelligence confirms just $159 stolen across attacker wallets so far.
- Systemic warning: Security leaders warn the attack exposes a structural weakness in open-source ecosystems.
A Breach at the Core of JavaScript
On September 8, the NPM account of developer Josh Junon, known as “qix,” was hijacked in what security researchers now describe as one of the most significant supply chain attacks to hit the open-source ecosystem. Malicious patch versions were quietly published to his packages, including chalk and debug, libraries that together account for a staggering two billion weekly downloads.
The injected code was anything but ordinаry. Security firms have identified it as a sophisticated “crypto-clipper” malware designed to intercept cryptocurrency transactions and replace wallet addresses with those controlled by the attacker. Although the NPM security team has since removed many of the compromised versions, the incident has already rattled developers and raised urgent questions about the resilience of open-source software.
The Phishing Campaign
The breach began with a phishing attack. Emails sent from a fraudulent domain—npmjs.help, crafted to look like the official NPM registry—warned developers that their accounts would be locked unless they updated their two-factor authentication (2FA) credentials.
“Please note that accounts with outdated 2FA credentials will be temporarily locked starting September 10, 2025, to prevent unauthorized access,” the message read.
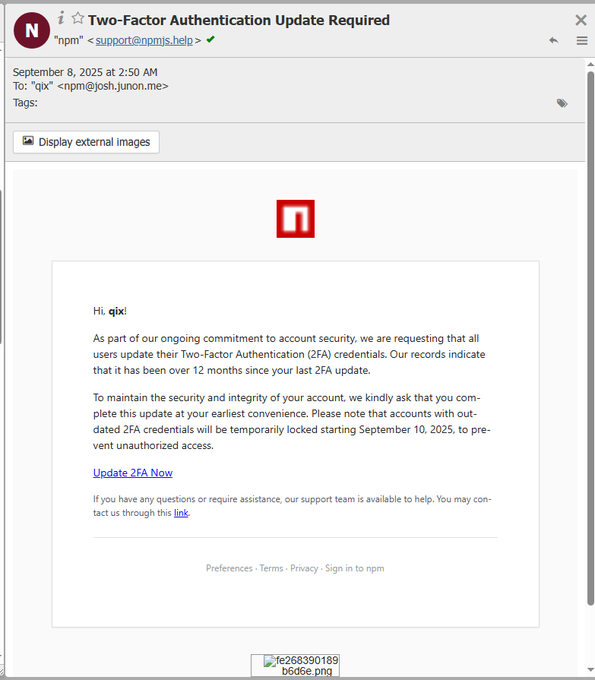
Junon later confirmed he was one of the victims. With his credentials in hand, attackers were able to publish poisoned updates that spread rapidly through the ecosystem.
Malware That Adapts to Its Victims
Researсhers analyzing the code say the malware deployed а two-pronged strategy:
Related: Binance Founder Zhao Says Lack of Privacy Hampers Crypto Payments Growth
- Passive Address Swapping: For browsers without a crypto wallet, the malware intercepted network traffic and replaced any detected cryptocurrency addresses with attacker-controlled ones. To avoid suspicion, it even used the Levenshtein distance algorithm to swap in addresses that looked visually similar to the originals.
- Active Transaction Hijacking: When a wallet extension like MetaMask was detected, the malware went further. It hooked directly into functions like eth_sendTransaction, intercepting transaction data before a user approved it. The wallet interface would still look legitimate, but the funds were silently redirected.
The malware targeted multiple blockchains, from Bitcoin (BTC) and Ethereum (ETH) to Solana (SOL), Tron (TRX), Litecoin (LTC), and Bitcoin Cash (BCH).
The Damage—Financially Small, Systemically Huge
Despite the staggering scale of the breach, the direct financial impact has been modest. Arkham Intelligence reported:
“There has been a total of $159 stolen so far in the NрM supply chain attack. These coins were sent to addresses tagged in the original write-up sharеd by Ledger’s CTO.”
The limited losses reflect two mitigating factors: most projects pin their dependencies, preventing automatic installation of compromised versions, and wallet-based attacks still require manual user approval.
Related: Kusama Reveals Details Of New AI Product in Recent Livestream
A Warning to the Ecosystem
Even with the limited financial losses, developers are treating this as a wake-up call. Kaal Dhairya, lead developer of Shiba Inu, urged caution in a statement on X:
“I’m seeing many protocоls turning this into a marketing stunt, claiming their portal is safe. You’re not truly safe until the attack’s full scope is determined. For everyone until then, review what you sign, pause transactions, and stay cautious.”
Meanwhile, DeFiLlama founder @0xngmi reminded teams that dependency management was a key line of defеnse: “Most projects pin their dependencies,” he noted, reducing exposure to newly released malicious versions.
What Comes Next
Developers are now being urged to audit dependencies immediately and use the overrides feature in package.json to lock affected libraries to verified-safe versions. But experts say this attack won’t be the last.
The NPM ecosystem, like other open-source infrastructures, relies on trust in a relatively small number of maintainers. When that trust is breached, billions of downstream projects are put at risk.
The attack, in other words, may have netted just $159—but its implications are worth far more.